Life insurance can be a daunting and complex subject for many individuals, but it is an essential aspect of financial planning and protection for your loved ones. Before delving into the products and personas of various life insurance policies, it is crucial to understand the basic terminology and different types available. Term life insurance and permanent life insurance, including whole life and universal life insurance, are the two primary categories of coverage, with each offering unique features and benefits. This guide aims to provide beginners with a clear understanding of the key terms and types of life insurance policies, empowering them to make informed decisions that will safeguard their financial future and loved ones.
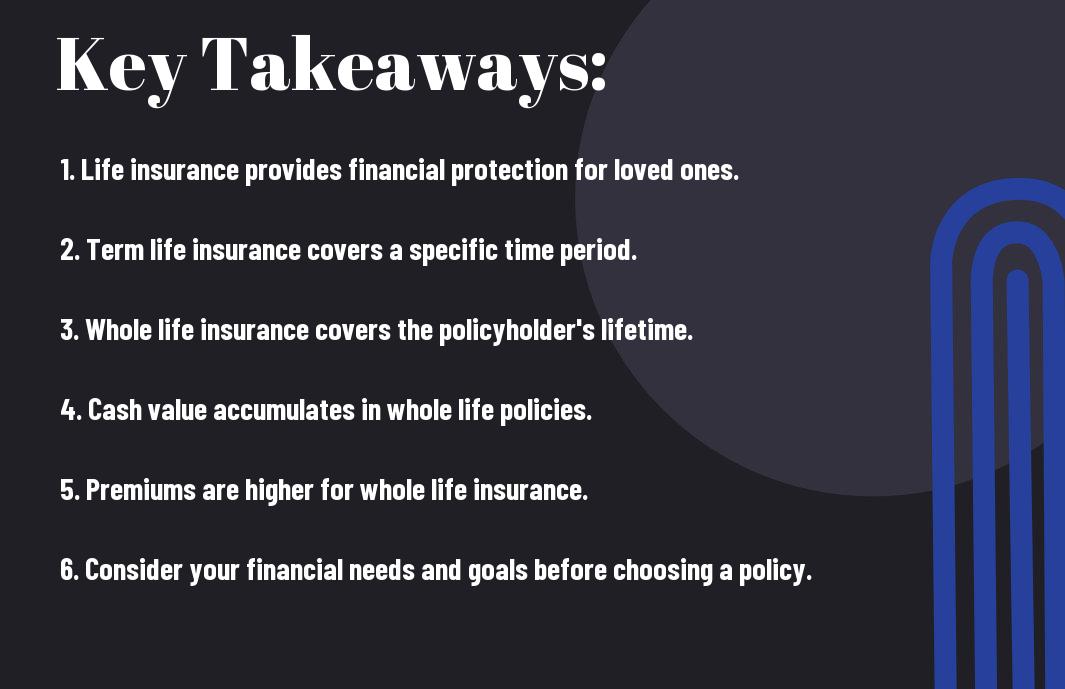
Table of Contents
Key Terms in Life Insurance
Some important key terms to understand in the world of life insurance include How To Buy Life Insurance, policyholder, beneficiary, premium, and death benefit.
Policyholders
For policyholders, it is crucial to understand that they are the individuals who own the life insurance policy. They have the authority to make changes to the policy, such as adjusting the coverage amount or naming a new beneficiary. Policyholders are responsible for paying the premiums to keep the policy in force.
Beneficiaries
Life insurance beneficiaries are the individuals or entities who will receive the death benefit when the policyholder passes away. It is important for policyholders to carefully consider who they name as their beneficiaries, ensuring that the benefit will go to the intended recipients in the event of their passing.
Insurance companies often provide the option for multiple beneficiaries or contingent beneficiaries, offering policyholders more flexibility in how the benefit is distributed. Policyholders should regularly review and update their beneficiary designations to reflect any changes in their personal circumstances.
Premium
Beneficiaries are not responsible for paying premiums, which are the scheduled payments made by the policyholder to the insurance company in exchange for coverage. Premiums can typically be paid on a monthly, quarterly, or annual basis, depending on the terms of the policy. The amount of the premium is determined by various factors, including the policyholder’s age, health, and coverage amount.
Plus, the type of insurance product and any additional riders or features added to the policy can also impact the premium amount. It is important for policyholders to understand the premium structure and payment schedule to keep the policy active and ensure continued coverage for their loved ones.
Death Benefit
An essential component of a life insurance policy is the death benefit, which is the lump sum amount paid to the beneficiaries upon the policyholder’s death. The death benefit provides financial security to the beneficiaries, helping them cover expenses such as funeral costs, outstanding debts, and ongoing living expenses.
Policyholders should carefully review the death benefit amount to ensure that it adequately meets the financial needs of their beneficiaries. It is crucial for policyholders to regularly assess and update their coverage to account for any changes in their beneficiaries’ circumstances or financial needs.
Types of Life Insurance Policies
For beginners, it is essential to understand the various types of life insurance policies available in the market. Here is a breakdown of the main types of life insurance policies you should be aware of:
| Term Life Insurance | Provides coverage for a specified term |
| Whole Life Insurance | Covers the insured for their entire life |
| Universal Life Insurance | Offers flexible premiums and an adjustable death benefit |
| Variable Life Insurance | Provides a cash value that can be invested in various accounts |
Term Life Insurance
With term life insurance, the insured is covered for a specific period, typically 10, 20, or 30 years. It provides a death benefit to the beneficiaries if the insured passes away during the term of the policy. Term life insurance is generally more affordable than other types of life insurance policies, making it a popular choice for young families or individuals seeking temporary coverage.
Whole Life Insurance
Life insurance provides coverage for the insured’s entire life, as long as the premiums are paid. It offers a guaranteed death benefit and also accumulates cash value over time. For instance, this cash value can be borrowed against or used to pay premiums. Whole life insurance is suitable for individuals who are looking for lifelong protection and investment potential.
For individuals seeking permanent coverage and guaranteed cash value accumulation, whole life insurance is a suitable option to consider.
Universal Life Insurance
Insurance offers the flexibility of adjusting premiums and death benefits to suit the insured’s changing needs. It also has a cash value component that accumulates over time. Universal life insurance is ideal for individuals who want some investment opportunities along with their life insurance coverage.
Insurance allows for a degree of flexibility and investment potential that may be appealing to individuals with evolving financial goals.
Variable Life Insurance
Life insurance policies offer a combination of life insurance and investment options. The cash value of the policy is invested in various accounts, providing the potential for higher returns. However, it also comes with the risk of investment losses. Variable life insurance is suitable for individuals willing to take on more investment risk in exchange for the potential for higher returns.
Policies combine life insurance with investment opportunities but also come with the potential for investment losses, making them suitable for individuals comfortable with risk.
Choosing the Right Life Insurance Policy
Now that you understand the basics of life insurance, it’s time to choose the right policy for your needs. This decision is crucial, as it will determine the financial protection your loved ones receive in the event of your passing.
Assessing Your Needs
With life insurance, it’s important to assess your needs based on your financial obligations, such as mortgage payments, loans, and the future needs of your family. Consider the amount of coverage necessary to support your loved ones in your absence, factoring in any existing savings and investments.
Understanding Policy Costs
Life insurance policies can vary in cost depending on factors such as age, health status, and the amount of coverage required. Understanding the different types of policies and their associated costs is essential in making the right decision for your financial situation.
Choosing the right policy involves a careful consideration of premiums, benefits, and any potential exclusions. It’s important to weigh the cost against the protection offered to ensure that your loved ones are adequately provided for in the long term.
Comparing Insurance Providers
On your journey to choosing the right policy, it’s essential to compare insurance providers to find the best fit for your needs. This involves researching and evaluating the products and services offered by different companies, as well as their reputation and financial stability.
| Criteria | Considerations |
| Available Policies | Term life, whole life, universal life |
| Financial Strength | Ratings from agencies such as A.M. Best, Standard & Poor’s |
| Customer Satisfaction | Reviews and ratings from policyholders |
Understanding the nuances of different insurance providers will help you make an informed decision based on reliable information and expertise.
Additional Considerations
After understanding the basic concepts of life insurance, there are additional factors to consider when purchasing a policy. It’s important to be aware of the various add-ons and riders that can enhance your coverage, as well as the potential tax implications of life insurance.
Life Insurance Riders
Considerations when selecting a life insurance policy include the option to add riders. Riders are additional provisions that can be added to a life insurance policy to provide extra benefits or coverage. Some common riders include accelerated death benefit rider, which allows the insured to receive a portion of the death benefit if diagnosed with a terminal illness, and a waiver of premium rider, which waives premium payments if the insured becomes disabled.
Tax Implications of Life Insurance
One important consideration when it comes to life insurance is the potential tax implications. Life insurance death benefits are generally received income tax-free by the beneficiary. However, any interest earned on the cash value of a permanent life insurance policy is subject to income tax. Additionally, if the policy is sold or surrendered, there may be tax consequences.
Any individual considering purchasing a life insurance policy should consult with a tax advisor or financial professional to fully understand the tax implications specific to their situation.
Understanding the Basics of Life Insurance – A guide to the key terms and types of life insurance policies for beginners.
Now that you have a better understanding of the key terms and types of life insurance policies, you can be more confident in making informed decisions about your coverage. Life insurance is an important aspect of financial planning, and knowing the basics can help you protect your loved ones in the event of an unforeseen circumstance. With this knowledge, you can choose the right policy that meets your needs and gives you peace of mind for the future.
 AIRMAX BLOG Portal Berita Terbaru AIRMAX BLOG
AIRMAX BLOG Portal Berita Terbaru AIRMAX BLOG


